Ever know the best ways to protect your company from cyberCrime. The most common form of Microsoft security alert scandal is caused by malware pop-ups on everyday websites that you can mistakenly view.
If you know how to download an app from the wrong site or play an online game, you can introduce potentially unwanted programs (PUPs) into your computer.
In addition to directing your web browsers to unsafe sites, programs record information about you and your system while spamming you through malicious pop-ups.
Some little to medium-sized organizations (SMBs) look at cybersecurity as an issue to be managed once their spending limit is somewhat bigger.
Lamentably, it is their organizations that are well on the way to be focused on cybercrime. 43 percent of cyberattacks target-independent ventures.
Crooks realize bigger enterprises have solid security frameworks, however littler organizations much of the time leave themselves helpless.
On the off chance that you run an SMB and cybersecurity isn’t yet a need, it’s an ideal opportunity to change that. Fortunately, there are things you can do to secure yourself, in any event, when assets are constrained.
The internet by the FBI’s Internet Crime Report, monetary misfortune from cybercrime in the only us was more than $1.3B in 2016.
So to help, there are 4 things you can do to fortify your protection from cybercrime.
Prominent information breaks at organizations like British Airway and Marriott get a ton of media inclusion, yet cybercriminals are progressively following local gatherings, schools, independent companies, and city governments.
Just in the Midwest. Medical clinics, libraries, voter enlistment frameworks, and police offices have succumbed to one sort of computerized commandeering or another.
Cybercrime isn’t only worrying for corporation innovation divisions. Schools, scout troops, Rotary clubs, and strict associations need to comprehend what to search for and how to deal with it.
10+ Best Ways to Protect Your Company From CyberCrime
As the scholastic executive of another cybercrime of another cybersecurity center at Indiana University, I’ll be assisting with driving understudies and employees in showing nearby, province, and state government offices, not revenue driven associations and private ventures how to improve their digital cleanliness.
They’ll figure out how to all the more likely oversee computerized frameworks, ensure their protected innovation, and improve purchase security.
Everybody should know the nuts and bolts for how to ensure themselves and the gatherings or associations they’re a piece of.
Here is a short glance at a portion of the cybersecurity how to protect your business from cyber crime we’ll be encouraging individuals from our networks to remember as they go online for work, play, or chipping in.
Actualize worker preparing
Workers who are undeveloped in inappropriate security rehearses are a colossal weakness.
It’s completely basic to prepare representatives to perceive notice indications of cybercrime, just as how to keep chances low in case, and there ought to be a framework set up for announcing indications of an assault.
One of the most widely recognized security dangers is phishing. The Henry M. Jackson Foundation, a clinical research charitable, attempted to teach workers by conveying counterfeit phishing messages now and again consistently.
At the point when the Jackson Foundation originally began actualizing these phishing – training efforts, the snap rate among representatives was around 27 percent.
Each time a representative tapped on the phony phishing email, they got a spring up clarifying was, in the long run, ready to get click rates down to around three percent.
Instructing representatives on security dangers ought to never be a one – time thing. Cybersecurity preparation ought to happen all the time to stay aware of the most recent innovation and guarantee new workers don’t make security vulnerabilities.
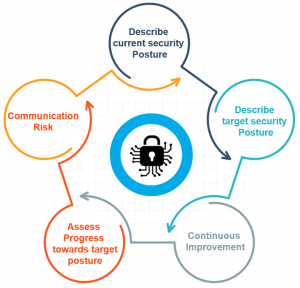
Make a framework security plan
A framework security plan (SSP) is a synopsis of all security rehearses that keep your information secure. The SSP distinguishes includes in a framework, for example, equipment, programming, safety efforts, preparing strategies, and episode reaction plan.
This record remembers subtleties for how to confine access to approved clients and guarantee representatives practice secure propensities and react on account of a security break.
It likewise keeps things from getting lost in an outright flood when timetables get going.
On the off chance that your IT staff has educated this matter, you can set aside cash by keeping things in –house, however something else, it’s smarter to contract an expert. A seriously composed SSP could wind up costing you more at last.
Keep programming refreshes
Numerous SMBs get too occupied to even think about ensuring their product is refreshed in an auspicious way, yet obsolete programming can open your organization to defenseless security imperfections.
Programmers regularly study the most recent programming refreshes to focus on those organizations that are behind in embracing them.
As indicated by Fortinet’s 2017 Global Threat Landscape report, 60 percent of composed security breaks focused on vulnerabilities that were at any rate 10 years of age.
Implement secure secret key approaches
Passwords ought to never be reused, and they ought to be refreshed continually. Basic passwords are likewise simple for programmers to break.
In 2012, a secret word breaking master uncovered a program that could work around any eight-character secret word.
This is the reason all passwords ought to be more than eight characters, and the more convoluted, the better.
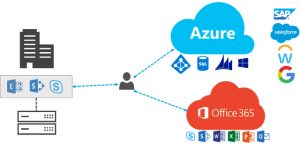
Redistribute cybersecurity
There are numerous assets you can go to if you feel overpowered at the ideal of overseeing cybersecurity issues yourself.
Numerous little organizations choose to put cybersecurity at the rear of their psyche since they don’t get it. Doing this could be your ruin, however.
Numerous IT organizations have some expertise in helping independent companies improve their security. Now and then a significantly less difficult choice is to utilize against malware or hostile to ransomware innovation.
As indicated by the look in to done by Verizon, 28 percent of security ruptures bring down security dangers.
Running an SMB is an unpleasant, tedious undertaking, so maintain a strategic distance from the compulsion to put cybersecurity on your organization’s heating surface.
Beginning today, focus on your business’ online security and you’ll be prepared for success (and less cerebral pains) over the long haul.
Stay up with the latest
Numerous ruptures, including 2017 one at the Equifax credit authority that uncovered the money related data of pretty much every American grown-up, come down to somebody keep from data programming running.
Most significant PC organizations issue standard updates to secure against recently rising vulnerabilities.
Keep your product and working frameworks refreshed. To make it simple, turn on programmed refreshes whenever the situation allows.
Likewise, make certain to introduce programming to check your framework for infections and malware, to find whatever may overcome. A portion of that assurance is free, like Avast, which Consumer Reports rates exceptionally.
Utilize solid, interesting passwords
Recollecting passwords, particularly confounded ones, isn’t fun, which is the reason such a lot of work is going into discovering better other options.
Until further notice, however, it’s essential to utilize one of a kind passwords that are distinctive for each site, and difficult to – hack things like “123456” or “secret word.”
Pick ones that are at any rate 14 characters in length. Think about beginning with a most loved sentence, and afterward simply utilizing the primary letter of each word.
Include numbers, accentuation, or images for intricacy on the off chance that you need, however, the length is increasingly significant.
Make a point to change any default passwords set is an industrial facility, similar to those that accompany your Wi-Fi switch or home security gadgets.
A secret phrase administration program can assist you with making and recollect mind-boggling, secure passwords.
Empower multifaceted confirmation
Much of the time, sites are requiring clients not exclusively to give a solid secret key yet in addition to type in a different code from an application, instant message or email message when signing in.
It is an additional progression, and it’s not great, yet multifaceted verification makes it a lot harder for a programmer to break into your records.
At whatever point you have the choice, empower multifaceted validation, especially for critical logins like bank and charge card accounts.
You could likewise consider getting a physical computerized key that can interface with your PC or cell phone as a much further developed degree of insurance.
Scramble and back up your most significant information
If you can, scramble the information that is put away on your cell phone and PC.
On the off chance that a programmer duplicates your documents, all he’ll get is hogwash, as opposed to, for example, your location book and money related records.
This frequently includes introducing programming or changing framework settings. A few producers do this without clients in any event, knowing, which improves everybody’s security.
For information that is critical, similar to clinical data, or crucial, similar to family photographs, it’s imperative to keep duplicates. These reinforcements ought to in perfect with your essential PC, and one remote, for example, in a distributed storage framework.
Be cautious utilizing open Wi-Fi
When utilizing open Wi-Fi, anybody close by who is associated with a similar system can tune in on what your PC is sending and accepting over the web.
You can utilize free programs like Tor, which was initially evolved to give secure interchanges to the US. The naval force, to scramble your traffic and disguise what you’re doing on the web.
You can likewise utilize a virtual private system to encode all your web traffic, notwithstanding what experiences your program – like Spotify music or video in the Netflix application – to make it progressively hard for programmers, or even easygoing clients, to keep an eye on you.
There is a wide scope of free and paid VPN choices.
In short: Be wary, proactive and educated
Obviously, there is substantially more an individual or association that can do secure private information. Web crawlers like DuckDuckGo don’t follow clients or their inquiries.
Firewall programming incorporated with the two Windows and Mac OS – or downloaded independently – can help prevent infections and worms from advancing into your frameworks.
To secure yourself against information breaks at places where your data is put away, you ought to think about freezing your credit, which squares anybody from applying for credit in your name without your authorization.
It’s free. If you have just gotten a notice that your information has been taken, consider putting a free “extortion alert” on your credit reports. AmazeInvent
There a lot of different sports to become familiar with cybersecurity as well, including some awesome web recordings.
No individual, association, or PC can ever be 100% secure. Somebody with the tolerance, cash, and expertise can break in to even the most secured frameworks.
Yet, by making these strides, you can cause it more uncertain that you’ll be a casualty, and in the process help raise the general degree of digital cleanliness in your networks, making everybody more secure both on the web and off.
Passwords
Change them normally and ensure they are solid. In any event 10, characters including images and numbers are perfect. Don’t simply utilize your name or “secret phrase” – which such a large number of individuals do.
A decent method to produce a solid one is to think about an expression or melody title and supplant a few letters with comparable looking images or numbers, for example, m1dn!ght@the0@$is (“midnight at the desert garden”). Change these routinely as well.
Make an IT strategy for staff
Having no IT use approach leaves you all the way to open abuse and security breaks. If you can bear the cost of the product, telling representatives you are observing their use is a major hindrance.
Likewise restricting staff from signing on to the organization’s Wi-Fi with unbound gadgets decreases some hazard.
Close by an IT arrangement, guarantee you have the correct programming to ensure your framework.
Limit access to specific records
Some of your online envelopes, for example, bookkeeping and finance frameworks, or even delicate R&D data ought to approach constrained to the individuals who need it and nobody else. This includes an extra layer of security to your significant business data.
Moreover, your business, as opposed to every representative is a suspect.
What is cybercrime prevention?
Top 10 Tips on Cyber Crime Prevention Use different username/password combinations for different accounts and avoid typing them.
Complicate passwords by combining letters, numbers, and special characters (at least 10 characters) and change them regularly.
How do companies protect themselves from hackers?
To the next level of cyber defense takers, companies also set up teams in their homes to monitor their security systems.
This means that companies invest in state-of-the-art hardware and software to keep them in server houses so that they can always stay on top of things and watch out for possible attacks.
What is an example of cybercrime?
Cybercrime, also known as computer crime, is the use of a computer as a tool to perform illegal activities, such as committing fraud, child pornography and trafficking in intellectual property, identity theft, or breach of privacy.
What is cybercrime, how does it happen, and how to prevent it?
Keep your software up to date
Updating your software is especially important for your Internet security software and operating system.
Often, cybercriminals use known exploits, or bugs, in your software to gain access to your system. Pursuing these flaws and exploits can prevent you from becoming a cybercrime target.